Visibility and Prioritization for What Actually Matters
What software is actually inside the systems we build and ship?
The industry has made progress with software composition analysis and SBOM generation for common ecosystems. But major blind spots remain. Many of the most critical systems in the world run on low level code and specialized package ecosystems that traditional tooling cannot see clearly.
That gap creates risk. It also slows response when vulnerabilities appear.
Today we are expanding The Manifest Platform to close several of the most persistent visibility gaps in software supply chain security. New capabilities bring deeper insight into C/C++ environments, Nix ecosystems, embedded software, and third-party binaries, while helping teams prioritize remediation based on real exploitability.
For security leaders and practitioners, the goal is straightforward: know what is in your software, know what actually matters, and respond faster when risk appears.
Why Software Supply Chain Visibility Still Falls Short
Many organizations believe they have software inventory under control. They run SCA tools, collect SBOMs from vendors, and track CVEs across development environments.
But those controls often focus on modern application ecosystems like JavaScript, Python, or Java. They rarely extend cleanly into areas such as:
- C/C++ codebases powering embedded systems
- Custom operating system layers
- Nix-based environments
- Third-party binaries without supplier SBOMs
These environments are common in industries such as automotive, healthcare, industrial systems, and defense. They are also environments where security visibility has historically been weakest.
Legacy build systems, fragmented package management, and opaque firmware pipelines make it difficult to generate trustworthy inventories of what actually ships in a product.
Without that visibility, teams struggle to answer basic questions when vulnerabilities emerge:
- Do we use the affected component?
- Where is it deployed?
- Is the vulnerable functionality reachable?
- Which supplier delivered it?
The result is familiar to most AppSec teams. Vulnerability dashboards fill with alerts, engineers scramble to patch everything, and organizations still lack confidence about their real exposure.
The Manifest Platform addresses this problem by expanding visibility where it has historically been missing.
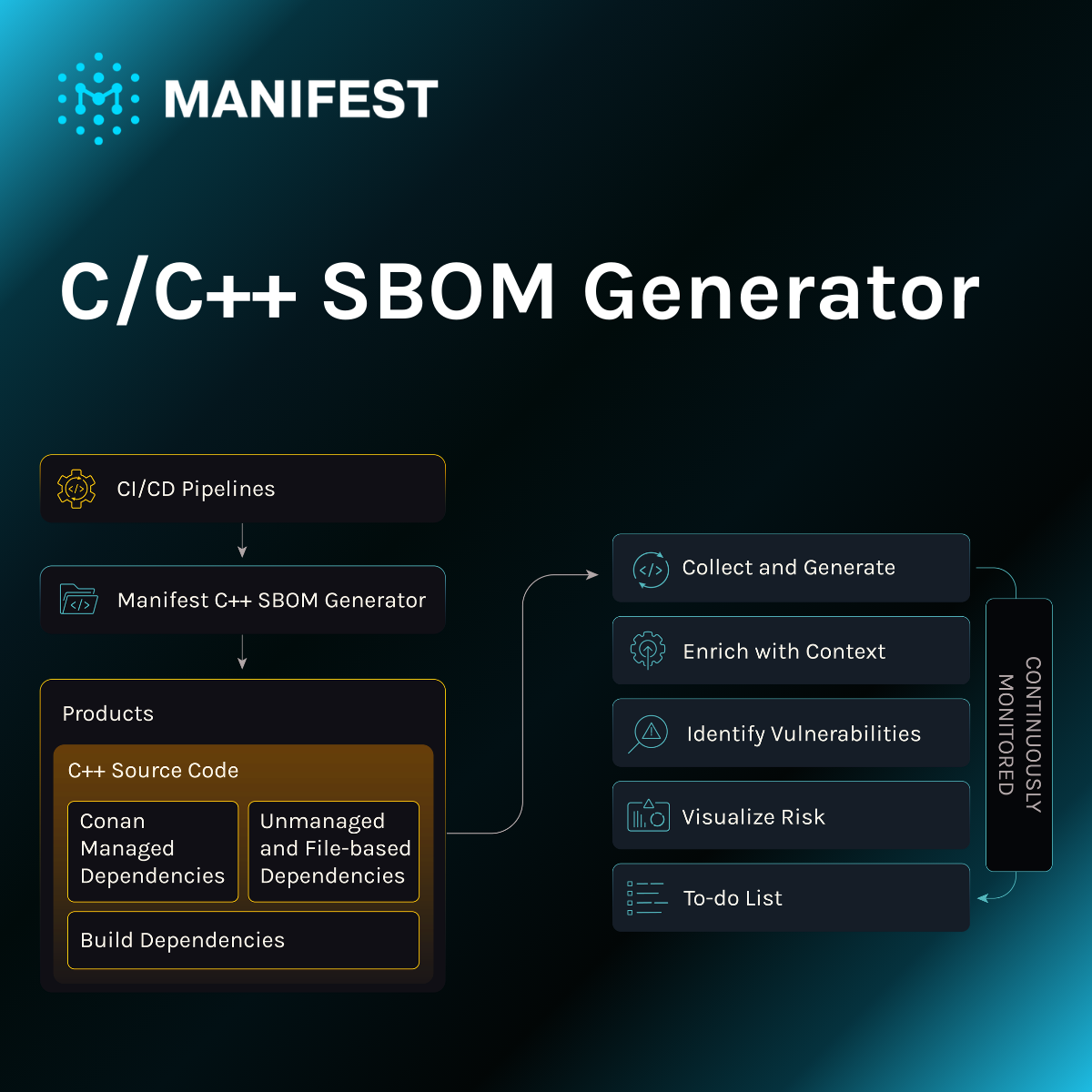
SBOM Generation for C and C++
C and C++ underpin many of the world’s most critical technologies. Vehicles, medical devices, industrial control systems, and defense platforms all rely heavily on these languages.
Yet generating accurate SBOMs for C and C++ environments has long been difficult.
Traditional tooling struggles with fragmented build pipelines, complex dependency resolution, and embedded system architectures. As a result, organizations often ship critical systems without a reliable inventory of their software components.
The Manifest Platform introduces a C/C++ SBOM Generator designed specifically for these environments.
This capability enables teams to generate, inventory, and scan accurate SBOMs for low level and embedded software.
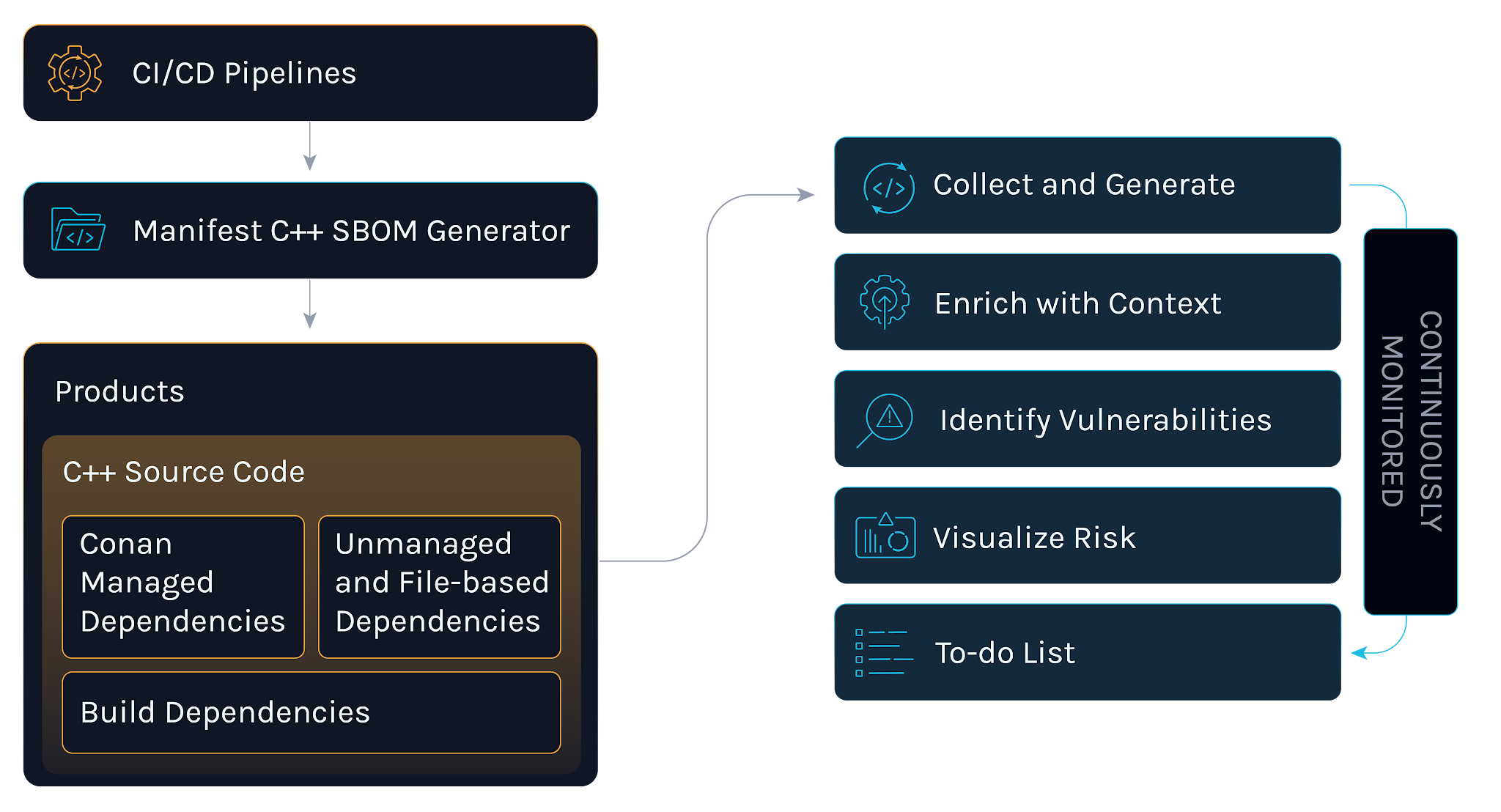
With the C/C++ SBOM Generator, customers gain:
Visibility for critical systems
Extend SBOM coverage into the low level components embedded in devices, appliances, and infrastructure systems where visibility has historically been weakest.
Faster risk response
Enriched SBOMs help teams quickly determine whether affected components exist in their software. This reduces time to assess exposure when vulnerabilities or business risks emerge.
Regulatory readiness
Accurate SBOMs help organizations meet increasing transparency requirements across regulated industries, including medical device premarket submissions that require detailed software supply chain documentation.
For organizations building or operating embedded systems, this visibility is essential.
Stronger Visibility Across the Nix Ecosystem
Another growing blind spot is the Nix ecosystem.
Nix provides powerful reproducibility and package management capabilities. It is widely used in secure development environments and infrastructure automation. But vulnerability visibility within Nix packages has historically been limited.
The Manifest Platform now provides automated vulnerability mapping for Nix packages, enabling security teams to track known vulnerabilities across their Nix-based environments.
This improves supply chain visibility for teams using Nix in production systems and helps ensure vulnerabilities do not hide inside reproducible build pipelines.
The platform also adds end-of-life and end-of-support (EOL/EOS) coverage across devices and software components, helping teams identify outdated software before it becomes a security liability.
Exploitable and Reachable Are Not the Same
One of the most common problems in vulnerability management is prioritization.
Most organizations rely on signals such as CVSS scores, exploit prediction scores, or asset criticality. These inputs are valuable, but they still leave a critical gap.
They do not tell you whether the vulnerable functionality is actually reachable in your application.
The Manifest Platform addresses this gap through reachability analysis, which evaluates whether vulnerable code paths can be invoked in your environment.
Instead of stopping at “component X contains a vulnerability,” reachability answers deeper questions:
- Is the vulnerable functionality used?
- Where does the code path appear?
- How could an attacker reach it?
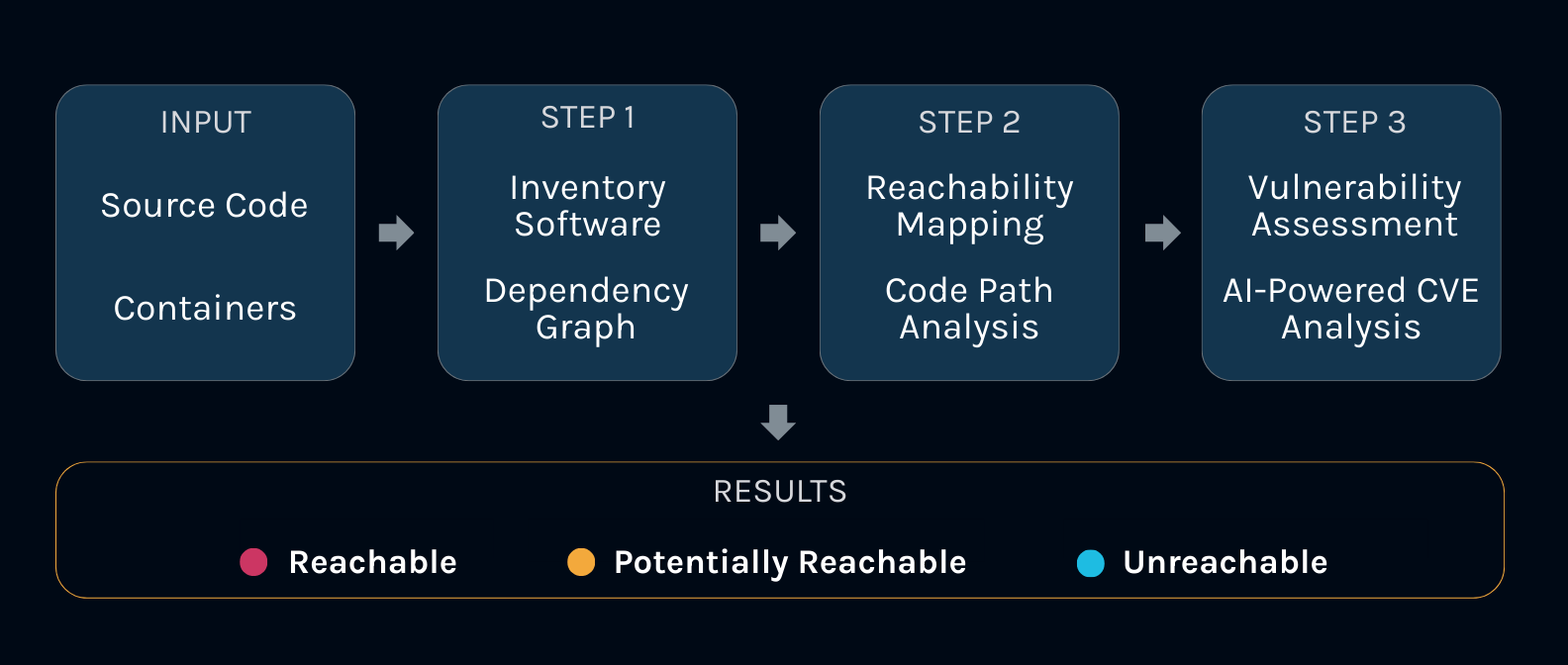
This helps security teams shift from theoretical risk to real exploitability.
The result is cleaner prioritization, fewer unnecessary patches, and faster remediation for vulnerabilities that genuinely matter.
Binary Analysis for Third-Party Software
Third-party software often introduces the largest supply chain risks.
Many vendors still cannot provide complete SBOMs. Even when they do, the SBOM may not match the compiled artifact that customers receive.
To address this, The Manifest Platform includes binary analysis capabilities that inspect compiled artifacts directly.
Binary analysis allows teams to generate SBOMs from executables, firmware images, libraries, and other build outputs. Instead of relying solely on supplier attestations, organizations can inspect what actually exists inside delivered software.
This capability enables several important outcomes:
- Visibility when suppliers cannot provide SBOMs
- Evidence based third-party risk management
- Faster exposure discovery when new vulnerabilities emerge
Real World Example: Visibility for a Smart Vehicle Platform
A global smart vehicle engineering team recently faced a familiar challenge.
Their vehicle platform relied on a public SDK provided by a third-party vendor. Documentation was limited, and the supplier could not provide a complete SBOM.
Security teams needed to understand what components were actually present inside the SDK before integrating it into production systems.
Using the Manifest Platform, the team analyzed the SDK and generated a detailed SBOM directly from the binary artifact.
This allowed them to:
- Identify embedded third-party components
- Map known vulnerabilities
- Establish a verifiable component inventory
The result was clear supply chain visibility for a software dependency that previously operated as a black box.
Governance for AI Models
Software supply chains increasingly include AI models alongside traditional code.
Open-weight models from repositories such as Hugging Face are often integrated into development pipelines with limited governance.
The Manifest Platform includes Manifest AI Risk, which continuously scans AI models, datasets, and licenses across the organization.
The platform performs daily assessments of open-weight models and custom models, helping teams maintain an up-to-date view of model risk across their environments.
For organizations adopting AI at scale, this ensures governance keeps pace with experimentation.
Seeing the Software Supply Chain Clearly
Software supply chain security ultimately depends on one principle: evidence.
You need reliable inventories of what exists inside your software, your infrastructure, and the components delivered by suppliers. Without that foundation, vulnerability management becomes guesswork.
The latest innovations in The Manifest Platform bring visibility into areas that have long been opaque, including C/C++ environments, Nix ecosystems, embedded systems, and third-party binaries. Combined with reachability analysis and AI model governance, these capabilities help security teams prioritize real risk and respond faster when threats emerge.
As software ecosystems grow more complex, the organizations that succeed will be those that can see their supply chain clearly.
See the Manifest Platform in action.

.png)

.png)